Designing hardware solutions for a fully encrypted future
Keeping data secret, even while it’s being used
In today’s digital world, sensitive information flows everywhere: from medical records and financial transactions to AI-driven services running in the cloud. Traditional encryption methods are already used to protect data while it is stored or transmitted.
But what happens when the data needs to be used? When data is stored in the cloud or in remote databases, performing computations typically requires sending queries to the server, where the data must first be decrypted before processing. This means that during execution, sensitive information is exposed in plaintext, creating a critical security vulnerability. Alternatively, data can be downloaded and decrypted locally, but this undermines the scalability and efficiency that cloud computing is meant to provide. In both cases, data becomes vulnerable precisely at the moment it is most valuable. With recent news such as the data breach at the test processing lab Clinical Diagnostics NMDL, the need for secure computations on encrypted data that ensures privacy is higher than ever.
What if we could compute on data without ever decrypting it? Fully Homomorphic Encryption (FHE) offers a solution by allowing the server to analyze the data while still encrypted. CogniGron’s PhD candidate Lingyu Gong is researching how this technology can transform the way sensitive data is processed, and what stands in the way of widespread adoption.
How does Fully Homomorphic Encryption work?
Homomorphic encryption can be divided into three main types: partial, somewhat, and fully homomorphic encryption. The difference between them is how much computation can be performed while the data is still encrypted:
-
Partial homomorphic encryption supports only one type of mathematical operation, either addition or multiplication, but not both.
-
Somewhat homomorphic encryption supports both operations, but only a limited number of times before it becomes unusable.
-
Fully homomorphic encryption (FHE) is the most powerful type: it allows unlimited calculations using both addition and multiplication.
Every computer programme, no matter how complex, ultimately reduces to combinations of addition and multiplication. Since all computer programs can ultimately be broken down into these two basic operations, FHE makes it possible to perform any computation on encrypted data.
FHE works through specific mathematical constructions, called schemes, which determine how data is encrypted, processed, and decrypted. Different schemes are optimized for different tasks: some schemes, such as CKKS, work well with real numbers and large datasets, which makes them especially useful for artificial intelligence, machine learning, and statistical analysis. Other schemes, like TFHE, are better suited for applications that rely on logical comparisons or decision-making processes. The ability to analyse encrypted blood test results, financial transactions, or AI training data without ever exposing them in plaintext represents a fundamental shift in data security.
So why isn’t everyone using it?
FHE offers many advantages, so why is it not yet widely used? The short answer: performance. FHE is significantly slower than conventional encryption methods, and requires more computational power which makes it more expensive.
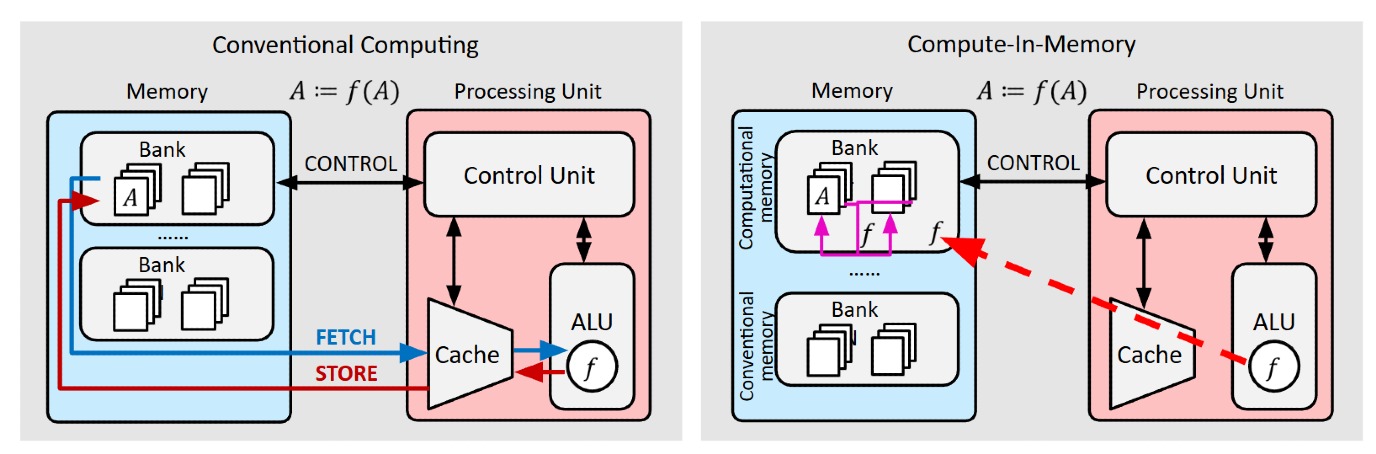
One issue is ciphertext size. Encrypted data is much larger than its plaintext equivalent, depending on the scheme and parameters used. Larger ciphertexts mean higher memory usage and more data movement. In traditional computer architectures, data constantly moves between memory, cache, and the arithmetic logic unit (ALU). With FHE, this movement becomes a serious bottleneck.
Another key issue is bootstrapping, one of the most important concepts in FHE. When encrypting plaintext, a small amount of noise (an error added on purpose) is introduced into the ciphertext. This noise is what ensures the security of the data. However, each homomorphic computation increases this noise. Once the noise exceeds a certain threshold, the ciphertext can no longer be decrypted correctly.
Bootstrapping is a process that refreshes the ciphertext by reducing the accumulated noise. It does not decrypt the data in the traditional sense. Instead, it re-encrypts the ciphertext into a new ciphertext with reduced noise. Importantly, it does this without revealing the underlying data. But bootstrapping is computationally expensive — and one of the main reasons FHE consumes so much time and energy.
Changing the game with innovative hardware
Lingyu’s research focuses on using specialized processors and hardware accelerators designed to perform FHE computations much faster and more efficiently than a normal processor (CPU). Using approaches like Computing-in-Memory (CIM) architectures, data can be processed where it is stored, reducing data movement and lowering energy costs.
Her team, led by Dr. Farhad Merchant (founder of CogniGron’s startup Ximplic), works with Field-Programmable Gate Arrays (FPGAs). These flexible chips can be programmed and reprogrammed to perform specific FHE calculations efficiently. These chips use on-chip memory Block RAM (BRAM): small, fast memory blocks built directly into the FPGA chip. By storing the encrypted data in this on-chip memory, the system doesn’t need to constantly retrieve data from slower external memory. In other words, instead of forcing conventional hardware to cope with FHE’s demands, the hardware itself is being reimagined.
Fully Homomorphic Encryption promises a world where hospitals can analyse patient data, companies can run safe financial services, and researchers can collaborate across borders, all without ever exposing sensitive information. At CogniGron, we’re rethinking the very relationship between algorithms and hardware — building systems that are secure by design and energy-efficient by necessity. Because the future of computing must not only be powerful. It must be private.

